
Key Takeaways
- The ModStealer Malware is designed to surpass and remain undetected by every major antivirus engine.
- The construct fits the description of “Malware-as-a-Service,” in which programmers offer associates with little technical know-how tools.
- Interestingly, hackers have been deploying new and innovative ways to fool the market participants and steal essential information.
The newly discovered ModStealer Malware strain poses serious threats to sensitive crypto wallet data, making investors anxious about their crypto holdings. The info stealer is designed to surpass and remain undetected by every major antivirus engine, according to Apple device security firm Mosyle.
ModStealer has been actively existing in the market for past one month, going unnoticed by any virus scanners. The malware is being spread by fraudulent recruiting adverts that targets developers. It circumvents signature-based defences and protectors by using a severely obfuscated NodeJS script.
The ModStealer discovery comes as the crypto market remains on edge with the rise of malware attacks. Hackers have been deploying new and innovative ways to fool the market and steal essential information required to sweep away millions in crypto wealth. Recently, hackers snuck malicious code into popular developer tools on npm, hiding the malware inside Ethereum smart contracts. By disguising it and using trusted platforms, they managed to avoid any detection, being largely unnoticed.
Why is The ModStealer Malware So Dangerous?
The code of the malware has been jumbled and loaded with methods and ways that prevent antivirus softwares from reading it. The encrypted code is such that it inhabits virus catching softwares that rely on signatures from reading it.
Since the detection of identifiable code is the foundation of the defences, the obfuscation stops them, enabling the script to run undetected. Using this lacunae, attackers can infiltrate a system with malicious instructions and evade traditional security scans, which often detect basic, unaltered code.
Additionally, ModStealer is a cross-platform malware that affects both Windows and Linux. This is in contrast to the majority of other malwares that mainly target Macs. The info stealer’s main objective is data exfiltration, and it is assumed that the code has pre-installed instructions to target 56 browser wallet extensions. This helps hackers retrieve credentials, private keys, certificates and even account information.
Further, the malware allows for remote code execution, screen capture, and clipboard hijacking. The code allows the operator to take almost complete control of compromised machines.
According to Mosyle, the construct fits the description of “Malware-as-a-Service,” in which programmers offer associates with little technical know-how pre-made tools. This year has seen a sharp increase in infostealers due to this model. In 2025 alone, Jamf reported a 28% increase in “Malware-as-a-Service” attacks in the crypto field.
ModStealer Incident Stays In Tandem With Rise in Crypto Malware And Hack Incidents
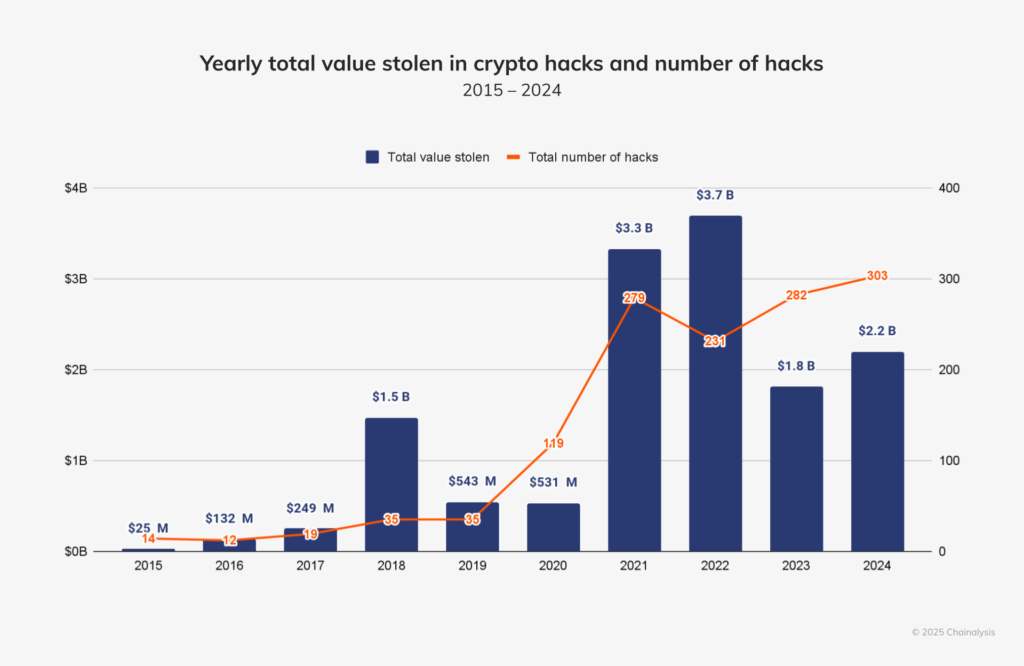
The ModStealer Malware is yet another example of the ongoing threats that the crypto industry is facing at the moment. Since its inception, the sector has been dealing with frequent hacks, scams and attacks that have tarnished crypto’s image in the industry.
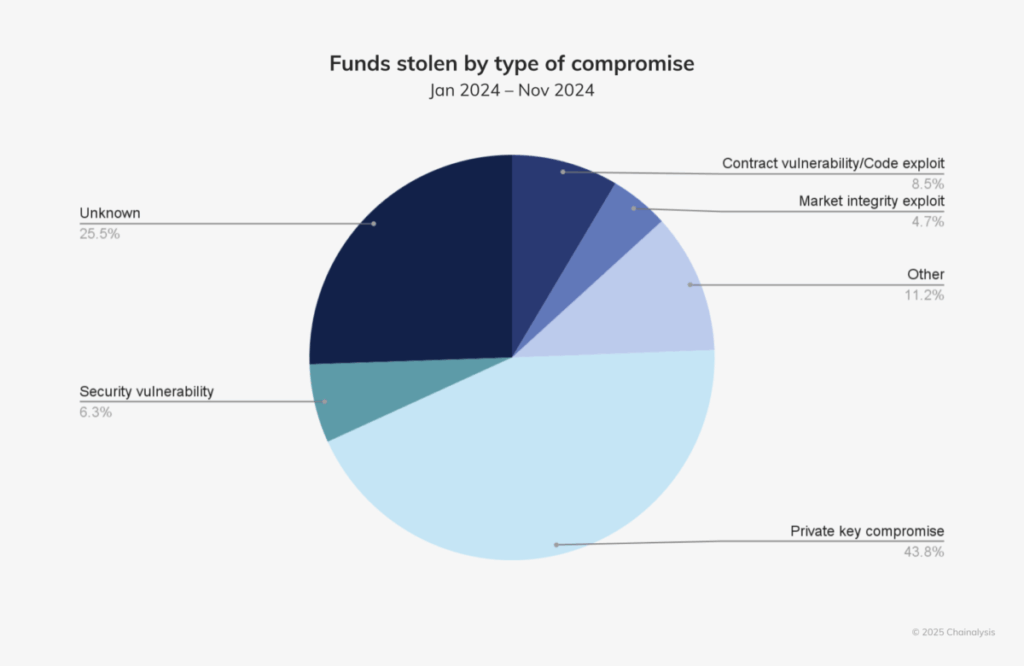
The rise in cyber attacks comes on the back of criminals stepping up their game. They mostly target the tools developers use to create crypto applications. Malicious code can be smuggled into platforms and software to gain direct access to crypto wallets and steal private keys and transaction data.
These attackers are clever and make sure they stay out of sight from people. Users and developers (both young and old in the crypto world) become victims of those threats. The excitement of the potential to be part of a fraud or security breach in crypto usually keeps investors on their heels! All of these incidences indicate the necessity of vigilance, auditing codes, and following protocols in the crypto world.



