
Cross-chain related ecosystems have recently suffered a large hack. Approximately USD 3 million has been stolen in a CrossCurve exploit using a major flaw in the bridge protocol’s smart contract code. The CrossCurve team has already responded to the incident by fixing the vulnerabilities involved, restricting the hackers from any access, and publicly identifying 10 Ethereum wallets linked to the hackers.
How the CrossCurve Exploit Unfolded
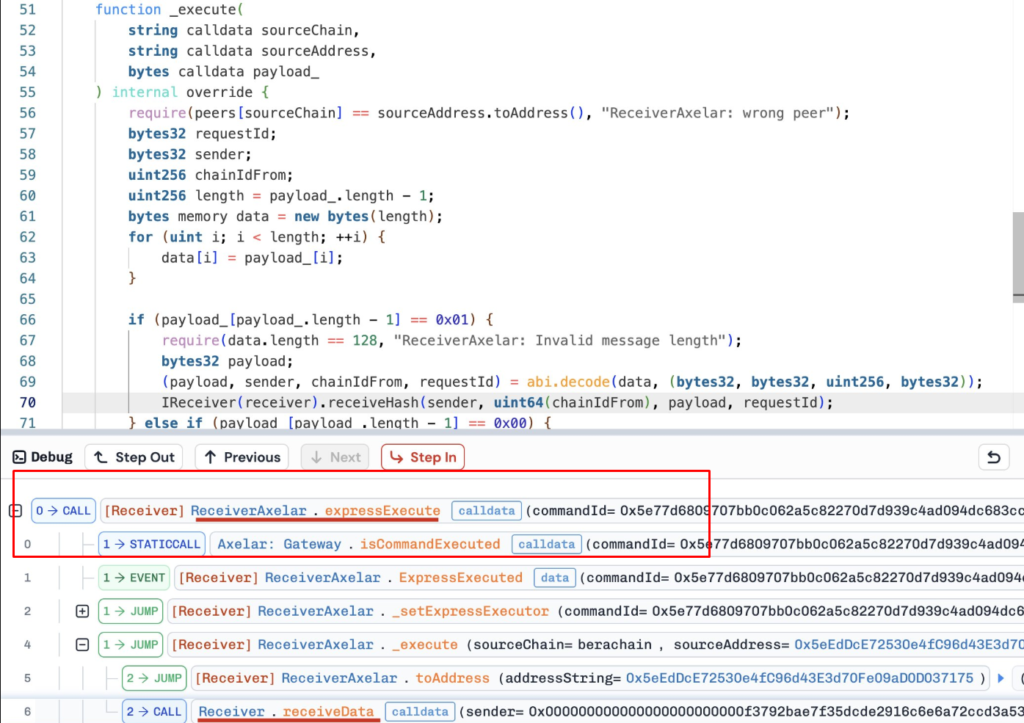
The CrossCurve exploit targeted a base flaw or missing security protocol in the bridge’s message validation system. The findings of the security code audit reveal that hackers were able to “fake” cross-chain messages and trick the protocol’s ReceiverAxellar contract into releasing funds from the bridge, without the required authentication (i.e., no collateral was left in the bridge). The hackers then drained the assets out of the bridge across multiple chains, including Ethereum and Arbitrum, at different times.
The vulnerability of the code exploits and the sophistication of the hackers are very similar to other attacks from the previous Bridge hacks. The complexity of securing messages across chains continues to be a difficult and persistent challenge. Sadly, this is just one more web3 incident, and it’s just starting the second month of 2026.
The Race to Recover Funds and Restore Trust
Boris Povar, CEO of CrossCurve, made a personal appeal for assistance from the wallets that received the funds. He requested that funds be returned within 72-hours at 10% of the value of the funds drained as a reward. The message indicates that no malicious intent was evident by the recipients of the funds; thus, suggesting they may be incidental “white hats” or users who copied a public transaction. Failure to comply with this request, the project intends to escalate the situation with law enforcement and provide evidence to exchanges to assist in freezing the assets.
In addition to taking these steps against the exploiter/ers, the CrossCurve team has actively worked with centralized exchanges (CEX) to freeze the stolen EYWA tokens and minimize the hackers’ ability to liquidate the tokens.



