
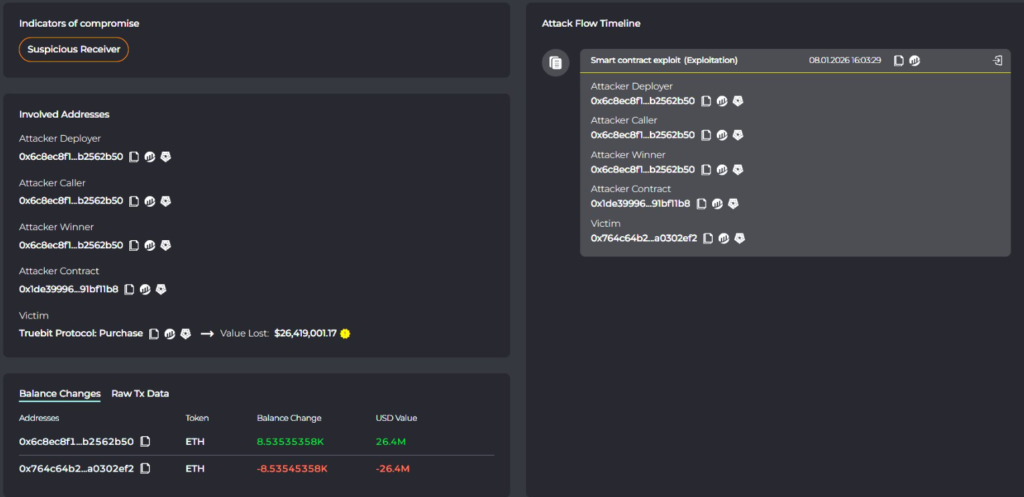
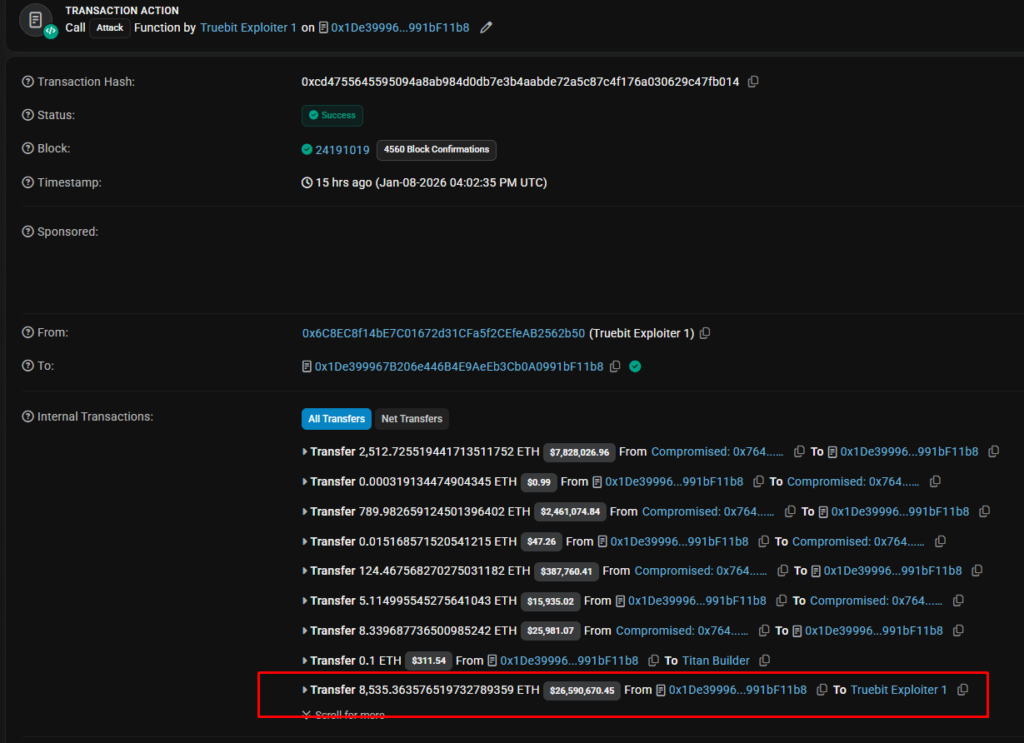
On January 9, 2026, the Truebit protocol suffered a devastating loss of $26 million when a vulnerability in an old smart contract allowed attackers to mint and steal large amounts of TRU tokens at very low prices. The vulnerability was in an old smart contract (0x764C64b2A09b09Acb100B80d8c505Aa6a0302EF2) that had been deployed five years earlier, and was identified and reported by cybersecurity teams like Cyvers Alerts, Lookonchain, and independent researcher Weilin Li.
How a Five-Year-Old Flaw Wiped Out a Token
The Truebit hack teaches a lesson about “DeFi archaeology.” The root cause of the exploit was a mispriced minting function in a legacy smart contract that was created five years ago. The flaw opened the door to an opportunity that allowed attackers to mint TRU tokens pretty much “for free.” As a result, almost 8,535 ETH worth of liquidity was drained out of the protocol.

Cyvers, a blockchain security company, monitored the creation of millions of dollars’ worth of tokens in real-time and reported that the attackers rapidly moved the funds through Tornado Cash.
Why This Incident is Important Beyond Just One Protocol
The Truebit disaster isn’t just an isolated incident; it reflects a pattern that exemplifies the systemic risk inherent in decentralized finance (DeFi): the forgotten code. As many protocols continue to innovate and evolve, older, unaudited smart contracts remain in existence and vulnerable.
This attack is indicative of a larger trend where criminals, possibly using sophisticated AI-based technology, are systematically targeting these historical vulnerabilities. Although crime rates in crypto have dropped slightly recently, this latest exploit provides brutal proof that a single unpatched vulnerability may be responsible for almost 100% of a project’s loss in value within a short period of time.



