
Just before the year ends, a severe Unleash Protocol exploit has led to a loss of around $3.9 million in user assets. The security breach occurred due to an assailant’s takeover of its governance system.
Governance Failure Leads to Massive Drain
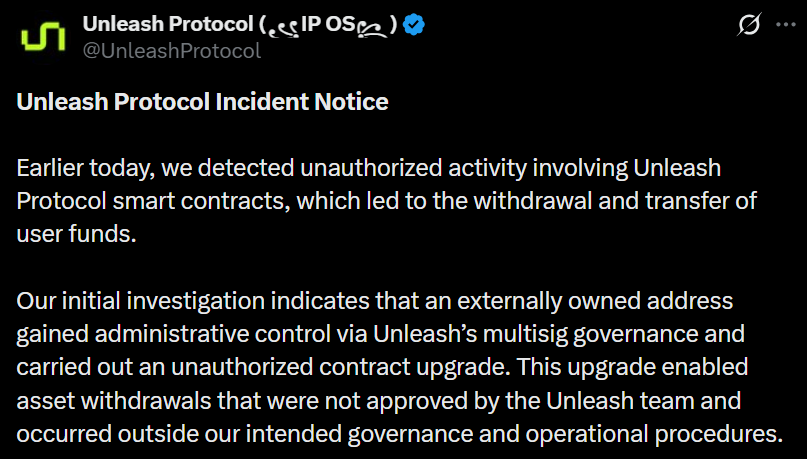
On Dec. 30th, hackers drained $3.9 million from an IP Finance solution. As explained in the platform’s incident report, an external address gained control of their administrator through successful manipulation of Unleash’s multisignature governance structure.
As such, the malicious actor was allowed to launch a modified smart contract which gave them access to withdraw funds from Unleash’s various contract accounts without undergoing the on-chain consensus and approval processes that govern the network. Among the different assets taken were WIP, USDC, WETH, stIP, and vIP tokens.
Read also: Trust Wallet Verification Set to Filter Flood of Post-Hack Claims
A Targeted Attack on Administrative Controls
The Unleash Protocol exploit showed how vulnerable decentralized systems are when it comes to administering access. In this situation, the problem was not because someone broke the smart contract code but due to a weakness in the permissioning/governance.

Once the attacker got hold of the funds, he was able to bridge the stolen funds to Ethereum and use more than 1337 ETH from Tornado Cash to hide his tracks. This platform has now stopped working entirely and has hired forensic specialists to determine how this happened, stating that the Story Protocol infrastructure remains intact.

Read also: Uniswap Governance Passes Historic ‘UNIfication’ Proposal, Triggers 100M Token Burn
Another Expensive Example of DeFi Security
The Unleash Protocol exploit demonstrates, once more, that even when you have strong technology in place, your administrative controls and governance provide the “key” to accessing technology and present the greatest risk to users as well.
As the investigation progresses, we are waiting to see if any retrievable funds can be reclaimed and how the protocol can work to restore user confidence after suffering a breach that attacked the heart of its operational security.
FAQs
What is Unleash Protocol?
The Unleash Protocol is an intellectual property finance (IPFi) platform built on the Story ecosystem. This application aims to tokenize IP rights (like media and brands) so they can be used as financial assets in decentralized applications (dApps).
How was the Unleash Protocol exploit executed?
In the Unleash Protocol exploit, the attacker gained control of the protocol’s multisignature (multisig) governance wallet. This allowed them to pose as an administrator, push a malicious contract upgrade, and then use that upgrade to withdraw user funds from the platform’s contracts.
Was there a hack on the contracts belonging to the Story Protocol?
There was not. Unleash maintains no signs that any of the Story Protocol underlying smart contracts, validators or other infrastructure had been hacked; only the governance and administrative control of Unleash was compromised in the breach.
Read also: Coinbase 2026 Outlook: Crypto’s Future Hinges on Derivatives, Prediction Markets, and Stablecoins



