
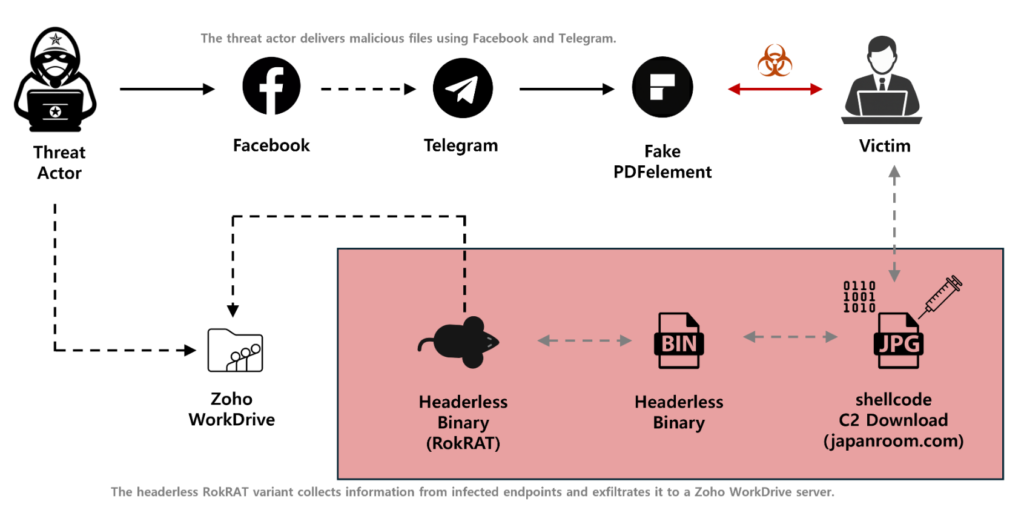
The APT37 North Korean cybercriminals have now started a new social engineering campaign using Facebook to distribute RokRAT malware. The hackers created two Facebook accounts (“richardmichael0828” and “johnsonsophia0414”) on November 10, 2025, to build up trust with their victims until they were ready to move to Telegram.
How the Attack Unfolds
The attackers employed a technique known as “pretexting” to manipulate their victims into trusting them by creating a false scenario. They claimed they had encrypted PDF files that contained sensitive military technical data and persuaded the victim to download and install a PDF viewer. The software was actually a version of Wondershare PDFelement but had been modified to run embedded shellcode when opened.
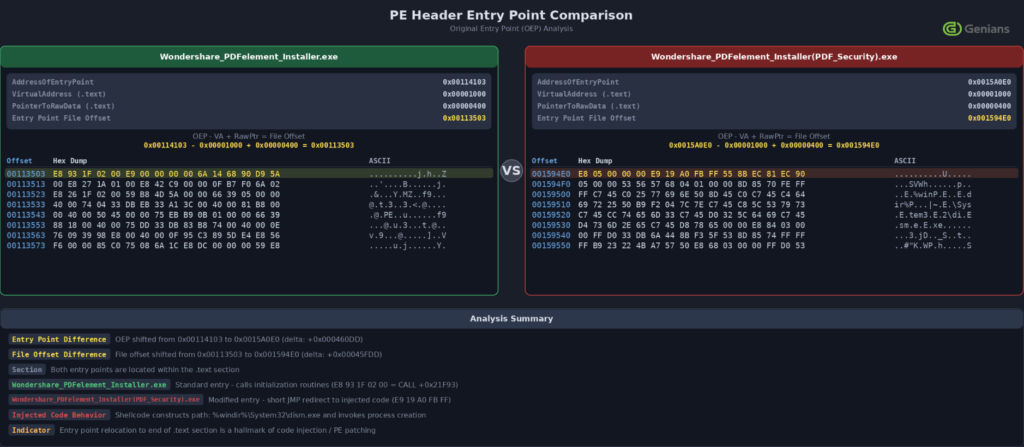
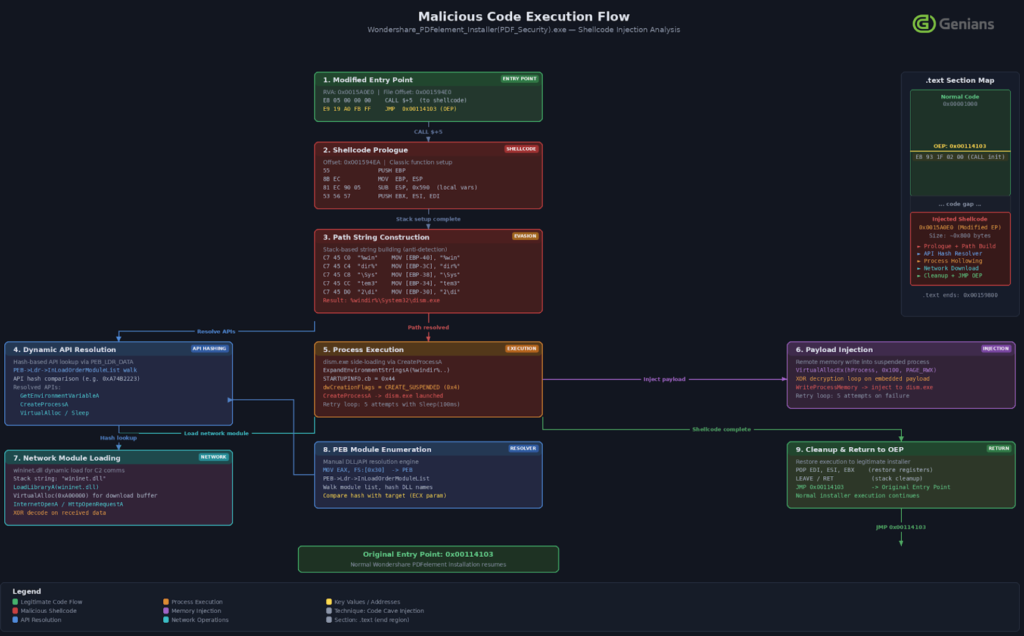
The malicious installer, “Wondershare_PDFelement_Installer(PDF_Security).exe,” lacks a valid digital signature; the entry point to run shellcode is located near the end of the .text section. The shellcode creates a new instance of “dism.exe” (a legitimate utility of Windows), injects the decrypted malicious code into it, and connects to the C2 server at japanroom[.]com. The .jpg extension is used to mask a normal image request, avoiding network monitoring and Uniform Resource Locator (URL) filtering.
The second-stage payload received by the victim as a JPG image (i.e., 1288247428101.jpg). After being XOR-decrypted [data restored to its original state using the eXclusive OR (XOR) logical operation] in memory, and executed filelessly. The final RokRAT malware payload utilized Zoho WorkDrive for its command-and-control channel and exfiltrated via hardcoded OAuth tokens (bearer credentials) screenshots, system information, and documents with the following file extensions: .DOC, .XLS, .PDF,.HWP.
Why This Matters for Crypto Security
Although RokRAT malware wasn’t created purely for crypto, how it gets into the system is of great concern to the digital asset industry because it is often socially engineered, and a compromised system can lead to stolen Application Programming Interface (API) keys, wallets, and/or exchange logins. Additionally, the use of legitimate cloud services, such as Zoho in this example, and fileless execution means traditional antivirus software will have difficulty detecting this type of malware.
Recently, a similar malware has been uncovered by security researchers, the EtherRat, which uses the EtherHiding mechanism, meaning it hides its command infrastructure in Ethereum’s smart contracts.
Next Step
Companies should focus their Endpoint Detection and Response (EDR)-based detection efforts on the following:
- Impairment of a machine’s ability to create abnormal processes immediately following the execution of legit software
- Installers spawning Script interpreters (PowerShell and CMD)
- External communications that do not fit within user context
- Periodic access to Zoho WorkDrive APIs
Employee training/awareness is also critical. Users must confirm the source of any software installation requests, even if they come from trusted social media contacts.



