
A single forged cross-chain message was enough to hand an attacker administrative control over the canonical bridged DOT ERC-20 contract on Ethereum and, within the same atomic transaction, convert 1,000,000,000 minted tokens into 108.2 ETH, worth approximately $237,000 at execution.
The exploit, executed via Hyperbridge’s gateway contract, is one of the cleanest examples of a bridge-layer attack in recent memory, which has no brute force, no prolonged probing, and no multi-step accumulation. Native Polkadot was not touched but instead, the mechanics of what happened on the Ethereum side demand a precise read.
The Attack Vector: Payload Validation Failure at the Gateway
Hyperbridge is positioned as one of the more technically sophisticated Polkadot-to-EVM interoperability solutions, built on the premise that cross-chain messages can be verified trustlessly by relying on cryptographic proofs of Polkadot’s consensus. That architecture, however, depends entirely on the gateway contract correctly validating inbound message payloads before acting on them.
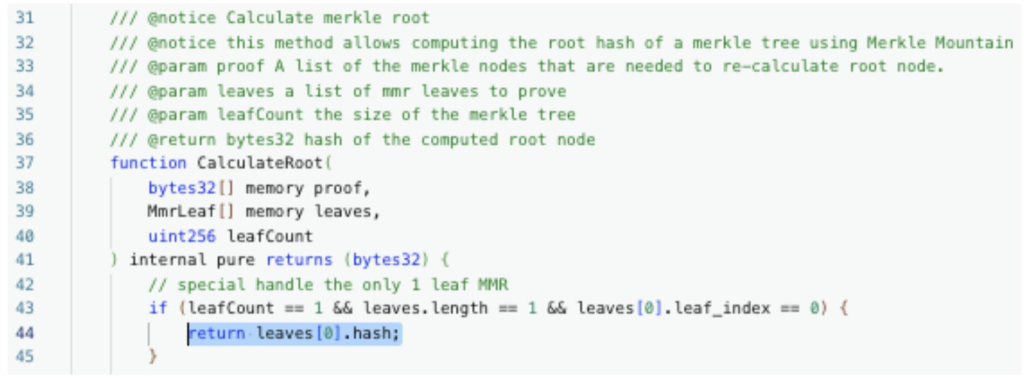
The root cause here was insufficient validation of inbound cross-chain payloads in the Hyperbridge gateway contract on Ethereum. The attacker crafted a message that was accepted by the gateway as legitimate Polkadot-origin data despite being forged. That single validation failure cascaded immediately into privilege escalation: the gateway contract processed the spoofed message and elevated the attacker’s address to admin-level access on the bridged DOT ERC-20 token contract.

At that point, the attacker held the same permissions as the protocol’s own deployer, including the ability to call the privileged mint() function with arbitrary parameters.
Three Transfers, One Atomic Sequence

The on-chain ERC-20 transfer log on Etherscan shows the execution in three clean steps, all within a single transaction.
The attacker minted 1,000,000,000 bridged DOT tokens out of thin air by utilizing the stolen admin access, sending them to an intermediate contract address (0x31a165a9…9067ca9AB). Those tokens were then routed to a second staging address (0x365084B0…601bAB5b8) before being deposited in their entirety into a Uniswap V4 liquidity pool. The pool had shallow ETH liquidity on the bridged DOT pair, which is exactly why the attacker chose it. Enough depth to convert the fabricated tokens into 108.2 ETH (~$237,000 in real value), but not enough to raise flags or trigger circuit breakers before the swap completed.
The entire sequence of message forgery, privilege escalation, mint, route, and swap is is executed atomically. There was no window for intervention once the transaction was submitted.
The $1.19 Billion Number Is Misleading: The Reason Behind It
The nominal mint value of $1,190,000,000 is technically accurate as a representation of 1 billion tokens at the prevailing price, but it has no bearing on what the attacker actually extracted. The real ceiling on damage was set not by the minting capacity of the contract, which was effectively unlimited once admin access was obtained, but by the ETH liquidity depth of the Uniswap V4 pool.
A low-liquidity pool absorbs sell pressure with steep price impact. The attacker’s 1 billion token dump moved through whatever ETH was available and stopped being profitable well before the nominal value was approached. The result was 108.2 ETH out of a pool that could not give more without the swap becoming self-defeating through slippage.
This is the structural constraint that separates a $237,000 incident from a catastrophic one. Had the bridged DOT/ETH pool carried significantly deeper liquidity, the same exploit mechanics would have produced a proportionally larger real-world extraction. The attack was not limited by the exploit itself; it was limited by available market depth.
Price Action: The Market Reaction

The 15-minute DOT chart records the market response with precision. The digital asset had been trading between $1.220 and $1.250 through most of April 12 before drifting lower into the early hours of April 13. The impact candle dropped price sharply from the $1.206 level to an intraday wick low of $1.150 a decline of roughly 4.6% within a single 15-minute window.
The RSI (relative strength index) on the 15-minute timeframe bottomed at 38.90 during the sell-off, pushing the oscillator into oversold territory, while the signal line sat at 27.61. As of the price action, DOT had partially recovered to $1.189 but had not reclaimed the $1.200 level, which now acts as the immediate resistance zone. With the RSI currently reading above its signal line, the oversold condition appears to be unwinding, though the recovery lacks any strong conviction so far.
The important context here is that the price action reflects information-driven selling by market participants responding to the exploit news, not any direct mechanism linking the Ethereum bridge attack to native DOT’s market structure. The relay chain was unaffected and the sell-off is a sentiment event, not a contagion event.
Exchange Response and Practical Implications
As a precaution, Upbit and Bithumb have both suspended bridged DOT deposits and withdrawals. Until the Hyperbridge gateway contract is patched and the full scope of the illegitimately minted supply is accounted for, exchanges have no reliable way to distinguish compromised tokens from legitimate ones.
For holders of native DOT, the event carries no direct protocol risk. Staking, parachain operations, governance, and relay chain consensus were all entirely outside the attack surface. The only exposure for native DOT holders is the price impact driven by market sentiment, which is already visible in the chart data above.
The Broader Pattern Bridges Cannot Escape
Hyperbridge was not marketed as a basic lock-and-mint bridge. It was positioned as an advanced, proof-based messaging solution that would bring a higher standard of security to Polkadot-EVM interoperability. The fact that a single crafted message was sufficient to bypass its payload validation and grant unrestricted minting privileges is a significant failure relative to that positioning.
The pattern here is that the forged message, escalated privileges, mint, and dump have shown up in enough bridge exploits throughout various protocols to constitute a known attack class. Yet the failure mode keeps recurring because payload validation at the gateway layer is simultaneously the most critical security checkpoint and the one most frequently under-audited in production deployments.
Bridges remain the highest-risk surface in cross-chain infrastructure, not because the underlying chains are insecure, but because every bridge introduces a new trust assumption about message authenticity that the chains themselves do not share. Native DOT’s safety in this incident is not evidence that Polkadot’s security model held; it is evidence that the attack never reached Polkadot’s security model in the first place.



