
The genesis of blockchain relied upon this principle of transparency: the records of each transaction, the state of the entire chain, and every smart contract run. Each of these is publicly accessible by any individual who has chosen to run a node on the network. The core choice in design resulted in the creation of trust. And in doing so, created an unsolvable barrier in any transaction involving users for whom on-chain transactions have to be private.
This is where FHE or Full Homomorphic Encryption, comes into the equation. It is not an “addition to the privacy layer of the existing chain.” Instead, it is “a full mathematical technique that allows one to compute on the encrypted data without having to decrypt the data before carrying out the computation.”
What FHE Actually Does
Data at rest, or data in transit, is what most systems use to protect it. But to use that data, one should be able to work on its decrypt process. This moment of “exposure” is what most privacy systems compromise.
With FHE, the entire process is taken care of. The user encrypts data on their machine, sends that ciphertext to a network or smart contract, computation is performed on the ciphertext, and the ciphertext returns still encrypted and only the owner of the key is allowed to decrypt it.
The math is based on ring learning with errors (RLWE), which is a form of lattice-based cryptography and is known to be secure from the quantum attacks. The fundamental idea is if Enc(a) and Enc(b) are encrypted versions of a and b, then through fully homomorphic encryption (FHE), a server can compute Enc(a + b) and Enc(a b) without ever knowing the values. As multiplication and addition are the fundamentals of any calculation, that means FHE can compute any computation if the data is encrypted.
The Blockchain Problem FHE Solves
When a DeFi trader sends a big trade into a public AMM, the position becomes known to all the MEV bots on the network before it gets finalized. It becomes clear what the borrower’s collateral ratio is to all liquidation bots monitoring every block. And the DAO voter’s opinion becomes known to the public, making them vulnerable to social engineering prior to the voting period closing.
We can’t consider these as the edge cases. Public blockchains still have the structural issues that have hindered DeFi’s institutional participation. Additionally, it also limits the use cases based on confidentiality.
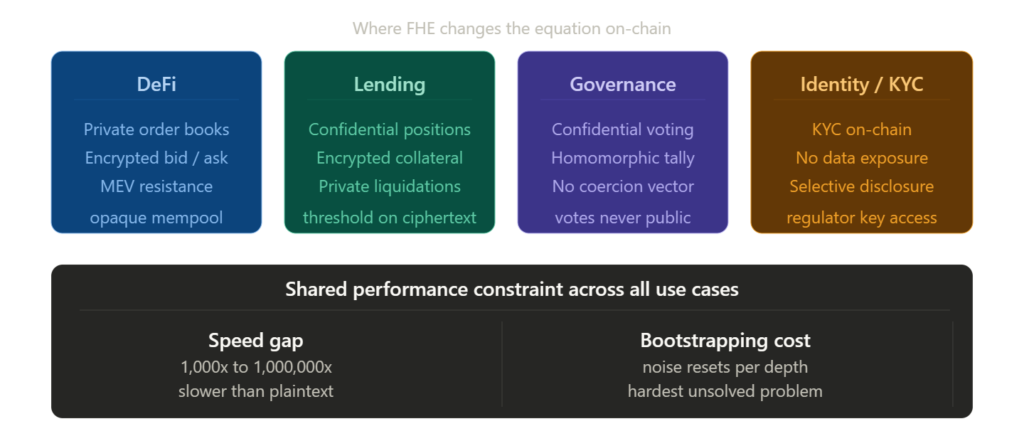
FHE addresses each:
- Private order books: encryption keeps bids and requests confidential. The matching engine works on ciphertexts.
- Confidential lending: the state of the positions are updated encrypted, and liquidation thresholds are computed without disclosing the actual collateralization ratio.
- Private governance: votes are encrypted, and the aggregates are computed homomorphically without knowing what each person voted for.
How It Works in a Blockchain Context
Traditional Smart Contract Execution vs FHE
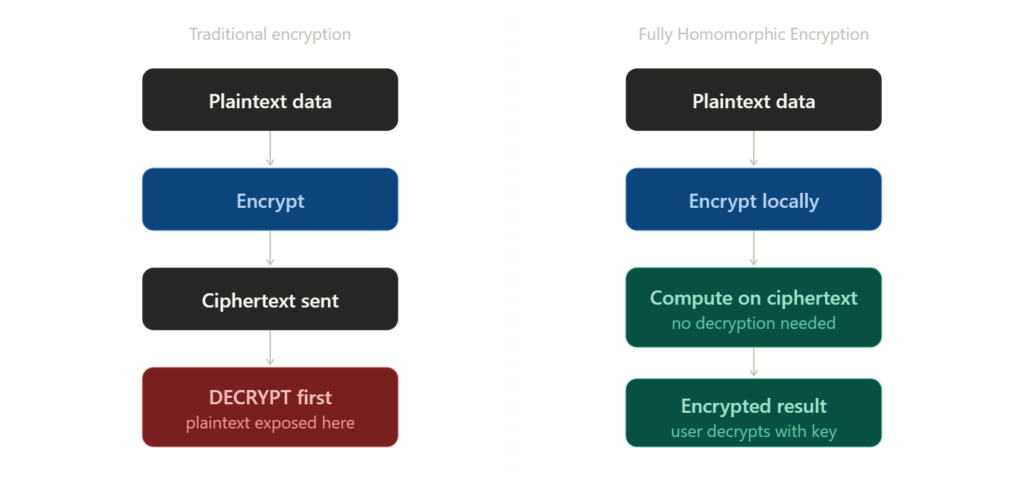
The plaintext user data enters into a traditional smart contract, the execution takes place in the clear state and the state is revealed in a public ledger. To ensure privacy, different techniques are implemented: zero-knowledge proofs for some statements or trusted hardware execution that relies on hardware assumptions.
In the second case, the operation of an FHE contract starts with the user encrypting the input with a public key on its own side, sending the ciphertext to the contract, and the contract working the ciphertext’s arithmetic, storing the result/returning it back as an encrypted ciphertext that only the key holder is capable of reading.
The Key Management Architecture
For key management, it is not possible for a single node to have the full key. The encryption key that is used by the smart contract works on the network level that is taken care of by a threshold decryption scheme. This prevents the execution environment itself from becoming a single point of compromise.
This is the threshold structure that distinguishes FHE blockchain implementation from data that is just encrypted and transmitted. Computations are performed on-chain in a verifiable way without any nodes accessing the plaintext value.
Who Is Building This
Both the concrete production stage and testnet stage are live. The fhEVM is Zama’s development, an addition of FHE opcodes to EVM so that Solidity developers can use encrypted integer types euint8, euint32, and euint256 by standard syntax while the costs for encryption and decryption are assumed at the protocol level. Fhenix is layered on top of the fhEVM as an Ethereum Layer 2 where transactions can use encrypted states and do not disclose them to validators even during execution. Inco Network is a Layer 1 that is FHE-native and designed for confidential computation.
What Comes Next
FHE cannot be termed an out-of-the-box replacement; it demands an overhaul in the way contracts are created and the way keys are managed and authorized for decryption events. The developer tool chain is at a very early stage and the security assumption for threshold key management is currently being tested with production environments.
It’s not about the cryptography, though. Craig Gentry presented the first fully homomorphic encryption scheme in 2009, the construction of which has been verified, debated by critics for over 15 years, and subsequently improved upon. The issue is about engineering and economics: Can the performance lag be closed sufficiently for FHE-native chains to be cost and time-competitive against native plaintext execution? And if so, before ZK proofs, could a parallel, competing primitive for privacy dominate the same institutional, compliance-minded segment?
ZK proofs and FHE can’t be termed as a competitive side; they can be considered as partners. ZK helps prove things about encrypted data without revealing the data itself; FHE helps compute arbitrary functions on encrypted data. High-end systems with the highest degree of privacy could utilize both.
The chains that work on the performance side problem first will inherit a specific and large pool of activity: institutional DeFi, private order books, compliant lending, and confidential governance. None of that activity is happening on public chains today, not because demand is absent, but because public execution is a structural barrier. FHE helps with the removal of that barrier.



