Since the beginning of 2025, a malicious campaign to distribute the ClipBanker malware (a clipboard hijacker trojan targeting crypto) via a fake Proxifier installer on GitHub has impacted over 2000 individuals, mostly based in India and Vietnam, according to findings from Kaspersky Labs.
Fake Proxifier Installer
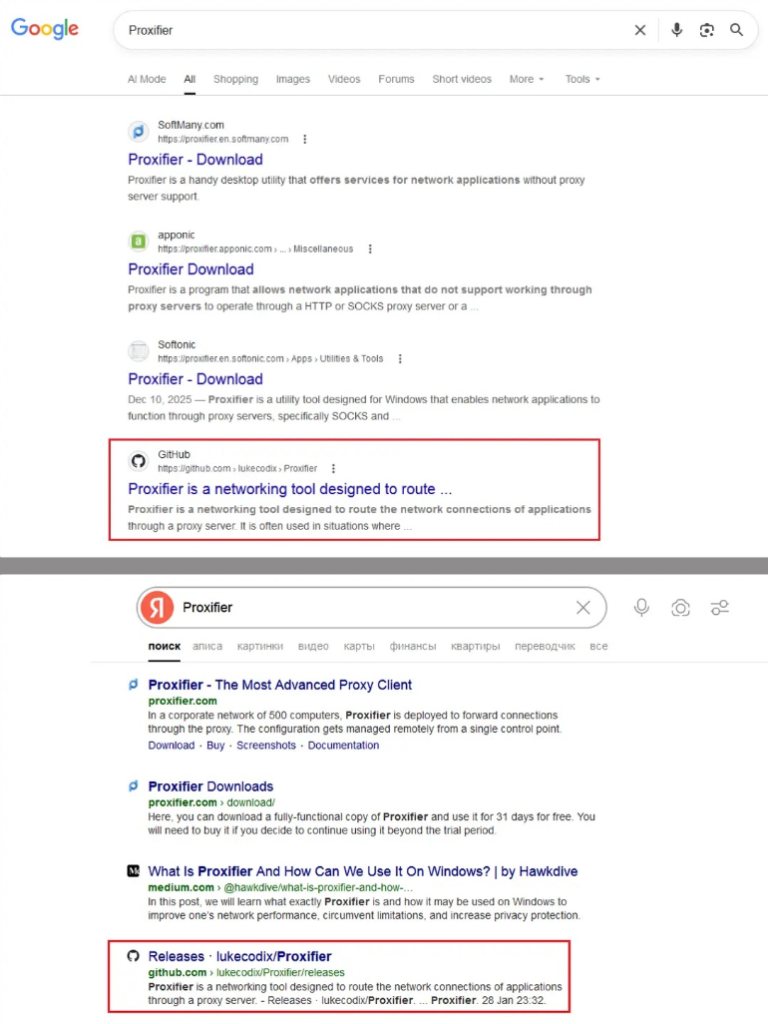
Attackers have optimized their GitHub repository for high ranking on search engines for “Proxifier.” The GitHub repository looks legitimate, as it displays source code for a very basic proxy server and has a downloadable zip file that contains an ‘exe’ file and an activation key for use with the executable. However, the file is a maliciously constructed wrapper around the legitimate Proxifier installer.
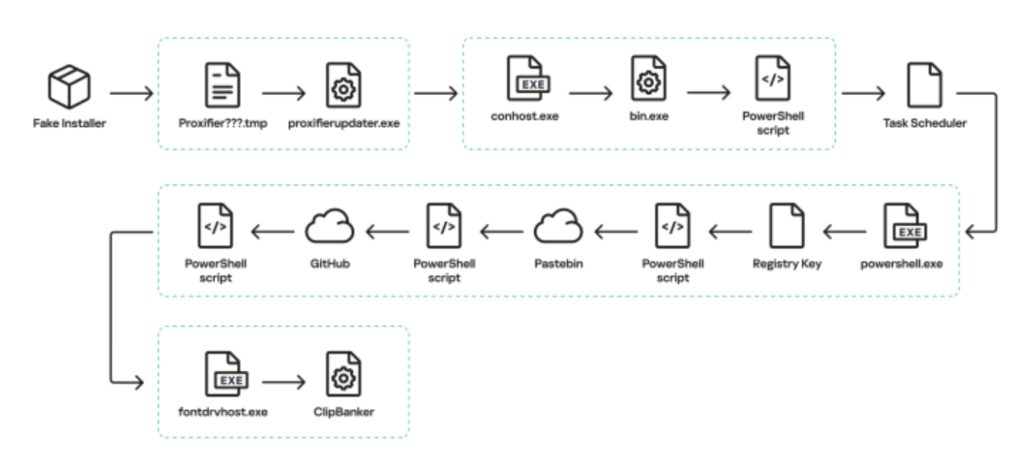
When the fake Proxifier installer is executed, it will run the real software in the foreground to keep the victim feeling comfortable while the fake installer drops a small stub file in the temp folder. A .NET application will then exclude TMP files and the current working directory from being examined by Microsoft Defender to ensure that future stages are executed without raising an alert. The malware exploits conhost.exe (which is a trusted Windows utility) to inject code before invoking an obfuscated PowerShell script entirely within memory (i.e., without leaving a trace on disk).
The PowerShell script will place an encoded trojan in the registry, create a scheduled task for persistence, and eventually download the ClipBanker malware. The ClipBanker trojan will then be injected into Fontdrvhost.exe to monitor the clipboard. When the victim copies a crypto wallet address, the ClipBanker will replace it with the attacker’s wallet address, causing all of the victim’s money to be redirected across 26 different blockchain networks.
Why It Matters for Crypto Security
This highlights how attackers have grown in creativity and sophistication when it comes to getting malware out to users. Clipboard hijacking appeared long ago; however, the creation of Fake Proxifier Inc. shows us that someone who was not that good at distributing malware is now very proficient. Using trusted platforms/repositories (e.g., GitHub) as attack vectors and fileless processes is causing traditional antivirus programs to be less effective than before, thus illustrating why you should verify the download source (even for software that appears to be open source).



