
Lazarus Group is using fake online meeting invitations to trick business users into infecting their own Macs with a newly identified malware kit called “Mach-O Man,” in a campaign aimed at stealing credentials, browser data and other sensitive information.
According to a report published by Any.Run, the attackers approach targets through Telegram, often by using compromised accounts belonging to colleagues or other trusted contacts. Victims are sent what looks like a normal meeting link and are directed to a fake page designed to resemble Zoom, Microsoft Teams or Google Meet. Once there, they are told they need to fix a connection problem by copying and pasting a command into their Mac terminal.
Instead of breaking in through a software flaw, the attackers get the user to run the command themselves, which makes the activity look like a normal user action and helps it slip past some traditional security controls.
How a Meeting Invite Became an Attack
The operation targets high-value business environments, especially fintech and crypto firms where Macs are commonly used by executives, developers and decision-makers, the report said. Once the malware is running, the attackers try to gather account credentials, browser sessions and information stored in macOS Keychain, which can open the door to company systems, software platforms and financial assets.
The stolen information is then sent out through Telegram, which the attackers use as a delivery and exfiltration channel. The report says that by the time the activity is spotted, credentials may already be stolen and sensitive data may already have left the organization.
How the Malware Works
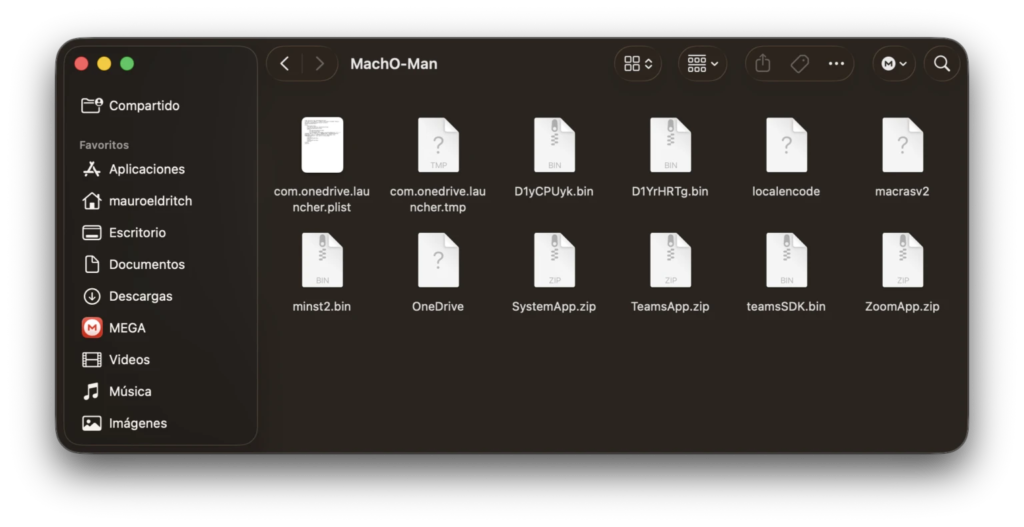
The report says Mach-O Man is made up of several parts that run in sequence. The first stage installs a fake app posing as a trusted meeting or system tool and repeatedly asks the user for their password. Behind the scenes, later components collect details about the computer, including system information, network settings, running processes and browser-related data.
Another part of the kit is designed to stay on the machine by setting itself to launch whenever the user logs in. The final stage acts as the main stealer, gathering stored browser credentials, cookies, Keychain entries and other files of interest, packaging them into an archive and preparing them for exfiltration. After that, the malware tries to delete itself and other components to reduce evidence of the attack.
Sloppy Code, Serious Threat
Even though the operation is dangerous, the report says some parts of the malware appear poorly written, as certain components can fall into endless loops, draining system resources and making the infection more noticeable to the victim. Researchers also found operational weaknesses, including exposed Telegram bot tokens and poorly protected command-and-control infrastructure.
Even so, the threat is serious because the attack does not depend only on complex software tricks. Instead, it works by taking advantage of ordinary business habits, pushing people to trust a message, react quickly and follow familiar steps without stopping to question them, giving the attackers a simple way in.
Why This Matters
The report makes clear that one infected Mac can create problems far beyond a single device. If attackers get hold of passwords, browser sessions and other stored data, they may be able to reach internal systems, cloud platforms and even financial accounts.
For companies, the danger does not stop with malware on one employee’s computer. It can lead to stolen accounts, leaked data and financial damage. The attack also shows how easily common tools, such as Telegram and fake meeting pages, can be used to fool employees when a message looks routine and arrives with a sense of urgency.



